 Bangalore, June 23:When whistleblower Edward Snowden “chatted” with the world on June 17 on The Guardian’s portal, it was in keeping with the epochal nature of the scoop. In terms of journalistic methods, the event set a new standard. After all, it is not often that a “source talks” directly to a media outlet’s audience.
Bangalore, June 23:When whistleblower Edward Snowden “chatted” with the world on June 17 on The Guardian’s portal, it was in keeping with the epochal nature of the scoop. In terms of journalistic methods, the event set a new standard. After all, it is not often that a “source talks” directly to a media outlet’s audience.
Snowden, in hiding from the most powerful surveillance apparatus in the world, obviously required a safe one-way line, through which he could communicate to journalist Glenn Greenwald.
So, how was this done? This may appear speculative, but interesting nevertheless.
Encrypted path
One safe assumption is that the link between Greenwald and Snowden was encrypted. The other end, connecting the readers to The Guardian’s server and Greenwald may have been “open”. But the connection between Snowden’s computer and The Guardian ran the risk of exposing his location. If this did indeed happen, how did he avoid being tracked? The answer may well lie in their understanding of cryptography in order to secure Snowden’s anonymity.
The fact that the “chat” was not “live”, that is, in real time is an important giveaway of the method. Normally, all participants in a live chat appear on the same server, which, from a security perspective, would be a giveaway.
A clue to what may have happened is revealed by Greenwald’s clarification in the #AskSnowden announcement on The Guardian website: “An important caveat: the live chat is subject to Snowden’s security concerns and also his access to a secure Internet connection.”
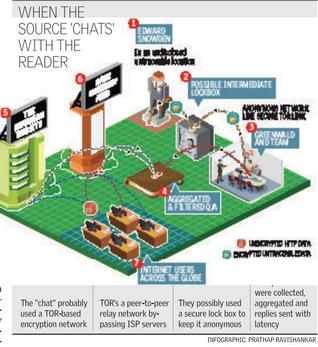
The architecture of network makes it possible for a snooper to track the path a computer takes if he/she has access to a node on the network of computers on the Internet. In case of the Snowden chat, Snowden was either directly or indirectly communicating with The Guardian server. This could have been achieved in many ways, but the most reliable method to ensure anonymity would have been to route the traffic of the interaction on a TOR-based encrypted network.
The Onion Router (TOR) project enables users to remain anonymous on the Internet. By design it is a peer-to-peer relay network; traffic is relayed from one user to another, instead of the routers and servers of the Internet Service Providers, who, incidentally, have been proved to be unreliable by Snowden’s very leaks.
Normally, when you are browsing, the source and destination of traffic is stamped on every packet of data of the user’s device. But Snowden would have done anything to avoid this to hide his trail.
Secure lock box
However, the TOR network is not infallible. The exit nodes or the last relays are indeed vulnerable and with a technique called ‘tagging attacks’, anonymity can be unveiled. A secure lock box may have been used to evade this (when two devices need to communicate, it can be accomplished by reading and writing securely into an intermediary device — the lock box server).
A cocktail of cryptography techniques and the use of a TOR network, combined with a good old fashioned passion for journalism is what must have made the Snowden interaction possible, when the world got its “source” firsthand.
